How to Clear False Codes and Stop Tool Compatibility Issues From Returning
You should start by validating data integrity and confirming codes match observable symptoms, then isolate real from phantom errors. Check cables, firmware, and tool interfaces for compatibility using a versioned matrix, and fix any mismatches. Implement automated, version-controlled checks across tools, logs, and configurations, and run regular tests with controlled scenarios. Maintain thorough change logs and rollback options to prevent drift. Consistent audits and propagation controls will reduce recurrence; more steps await to keep you ahead of issues.
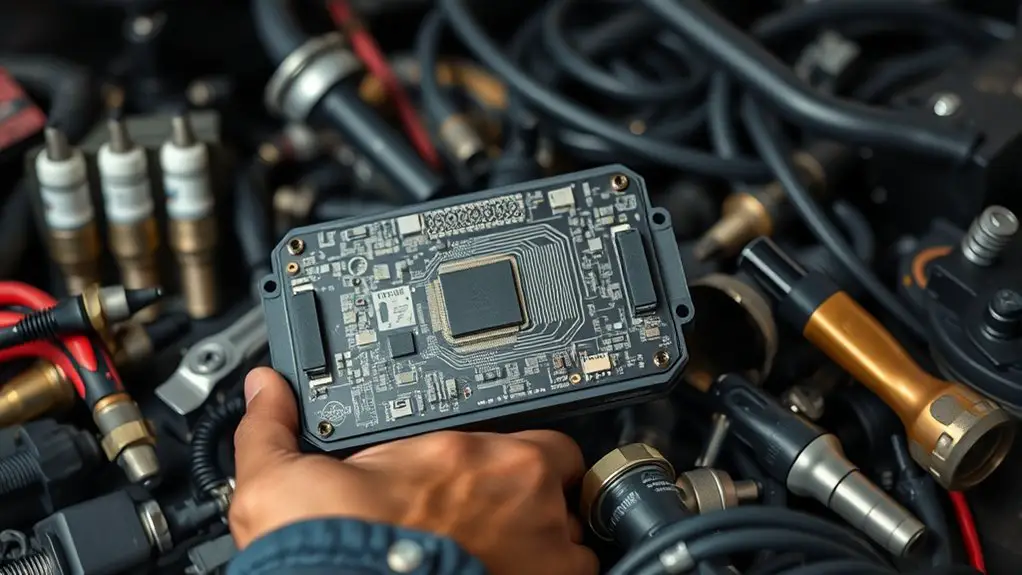
Understanding False Codes: Where They Come From and How to Spot Them

False codes aren’t random glitches; they stem from specific issues in how your device reads data, interprets signals, or processes inputs. You’ll spot them by tracing when the code appears, noting timing, source, and symptoms. Begin with data integrity: check cables, connectors, and firmware versions for compatibility gaps or degraded links. Next, verify sensor inputs and signal conditioning—noise, grounding faults, or offset drift can mimic genuine faults. Diagnostic strategies rely on reproducibility: can you recreate the code under controlled conditions, and does it disappear with a reset or parameter change? Use baseline comparisons to differentiate legitimate faults from transient anomalies. Examine error logs for recurring patterns, sequence gaps, or unexpected values. Keep your approach methodical: isolate modules, document every test, and avoid jumping to conclusions. Remember, false codes reflect misreads or misinterpretations, not absent problems. Your freedom comes from disciplined diagnosis, informed adjustments, and confidence in accurate problem framing.
Distinguishing Real Vs Phantom Errors in Tooling Systems
When tooling systems throw alarms, you must treat every alert as a hypothesis to test rather than an outright fault, because real errors and phantom signals often mirror each other under changing loads and conditions. You’ll pursue error identification with discipline, using targeted troubleshooting techniques and diagnostic tools to separate signals from noise. Begin with detection methods that quantify anomaly frequency, duration, and impact, then map causes to observed behavior. Real errors reveal persistent, reproducible patterns; phantom errors fade under stable conditions.
| Category | Signals to Observe | Actions to Take |
|---|---|---|
| Real errors | Consistent deviation, reproducible fault | Isolate module, verify power/communication, collect logs |
| Phantom errors | Intermittent, non-reproducible spikes | Reproduce under test stress, inspect sensors, rule out noise |
| Diagnostic approach | Cross-checks, root-cause tracing | Correlate data, perform controlled resets, document findings |
Error analysis emphasizes correlation, not guesswork. Use this framework to prevent misdiagnosis and reduce recurring failures.
Quick Diagnostics: Initial Checks to Validate Codes

Building on the prior framework for distinguishing real from phantom errors, quick diagnostics start with straightforward, initial checks to validate codes. You’ll verify that the reported codes match observable symptoms and recent events, ensuring a solid baseline before deeper dives. This step focuses on accuracy, not assumptions, so you can proceed with confidence and retain control over your tooling environment.
Start with quick, concrete checks: verify codes align with symptoms and recent events to establish a solid baseline before deeper dives.
1) Confirm code format and associated data, ensuring there’s no corruption or misinterpretation.
2) Cross-check timestamps, event context, and recent actions to rule out coincidental coincidences.
3) Reproduce the issue in a controlled scenario to observe whether the code persists under known conditions.
4) Document findings succinctly, distinguishing confirmed codes from ambiguous signals for subsequent review.
Verifying Tool-Side Compatibility: Firmware, Software, and Interfaces
Before you dive deeper, verify tool compatibility by validating firmware, software, and interfaces against the target codes and expected workflows. You’ll methodically confirm that firmware updates, interface protocols, and software synchronization align with the defined compatibility matrices. This prevents drift between tool behavior and code expectations, reducing false positives and rework.
| Column A | Column B | Column C |
|---|---|---|
| Firmware updates | Interface protocols | Software synchronization |
| Validation checks | Documentation alignment | Error handling parity |
| Version parity | Backward compatibility | Change-log traceability |
| Test results | Predictable responses | Recovery readiness |
Approach each item with a concise, testable criterion: confirm version numbers match the compatibility matrices, verify interface protocols match supported handshakes, and ascertain software synchronization preserves state across updates. When gaps emerge, document precise remedies and revalidate. Maintain discipline in firmware, software, and interface checks before proceeding with codes, guaranteeing freedom to operate without hidden regressions. This structured due diligence keeps tool behavior predictable and minimizes recurring compatibility issues, while empowering you to move forward confidently.
Establishing a Robust Testing Routine for New Tools and Updates
Set a consistent testing cadence that matches your release cycle, so you catch issues early and regularly validate changes to new tools and updates. Run rigorous compatibility checks for each tool version and update, ensuring firmware, software, and interfaces align before deployment. Prioritize clear, repeatable procedures for evaluating testing outcomes and documenting results to sustain confidence across teams.
Testing Cadence
A robust testing cadence combines scheduled checks, safe rollouts, and quick feedback loops so new tools and updates can be evaluated without disrupting current operations. You’ll set predictable intervals, define clear triggers, and document outcomes to maintain momentum while preserving stability. By aligning testing frequency with risk, you stay proactive rather than reactive, catching issues early and minimizing fallout. Use consistent testing methods that yield comparable results across versions, so improvements are measurable and repeatable. This cadence empowers you to balance speed with reliability, giving you freedom to innovate without chaos.
- Schedule-default checks at regular intervals and after major changes
- Apply staged rollouts with rollback points and clear success criteria
- Use standardized testing methods to collect comparable metrics
- Review results promptly and adjust cadence as needed
Tool Compatibility Checks
Tool compatibility checks begin with a precise, methodical evaluation of each new tool or update against your existing stack, so you know exactly how it will perform in production. You’ll run compatibility testing to verify interfaces, dependencies, and performance ceilings, then map potential error detection gaps before rollout. Plan a sandboxed experiment, document failure modes, and set rejection criteria if criteria aren’t met. This routine protects your freedom to iterate without fear of regressions.
| Tool | Test Focus | Outcome |
|---|---|---|
| Tool A | API compatibility | Pass/Fail |
| Tool B | Dependency drift | Pass/Fail |
| Tool C | Performance under load | Pass/Fail |
| Tool D | Error handling | Pass/Fail |
| Tool E | Rollback readiness | Pass/Fail |
Configuration Management: Keeping Settings Aligned Across Tools
You should start by establishing clear alignment of tool settings across environments to guarantee Cross-Tool Consistency. Define Change Propagation Rules so updates in one tool trigger coordinated updates elsewhere, minimizing drift. Then implement automated checks to verify that Align Tool Settings remain synchronized as you scale workflows.
Align Tool Settings
Aligning tool settings is essential to prevent drift between environments and guarantee consistent results. You’ll center on aligning configurations across platforms, ensuring you don’t fight drift later. Focus on practical steps that empower you to act with confidence, not guesswork.
1) Establish a single source of truth for tool calibration and settings synchronization, then mirror it everywhere.
2) Regularly audit configurations, documenting any deviation and restoring from the baseline promptly.
3) Implement automated checks that flag mismatches before they affect results.
4) Version-control configuration files and maintain change logs to track intent and impact.
Cross-Tool Consistency
When you’re aiming for cross-tool consistency, start by establishing a unified configuration model that defines common settings, formats, and validation rules, then apply it across every tool in your workflow. You’ll lock in predictable behavior by codifying defaults, error handling, and naming conventions so every component speaks the same language. Embrace tool standardization to reduce surprises during builds, tests, and deployments, and document deviations only where necessary. Implement integration protocols that enforce versioning, backward compatibility, and change tracking, ensuring updates don’t fracture compatibility. Schedule regular audits to verify alignment, and automate checks to catch drift before it surfaces as a problem. Stay proactive, minimize friction, and keep momentum by treating consistency as a shared responsibility across teams and tools.
Change Propagation Rules
Change propagation rules define how configuration changes travel from a source of truth to every dependent tool and environment. You’ll map every modification’s path, set containment gates, and guarantee you’re notified when drift occurs. By design, you anticipate change impact and embed feedback loops that surface conflicts before they cascade. Your adjustments stay deliberate, guided by reproducible steps rather than guesswork, so teams can act with confidence across ecosystems. Implementing these rules empowers freedom through predictability, locking in alignment while permitting safe experimentation.
- Identify change impact across tools and environments.
- Define adjustment strategies to resolve drift quickly.
- Automate propagation with verifiable checks and rollbacks.
- Review and refine rules after each release for continuous alignment.
Preventive Practices: Documentation, Change Logs, and Routine Audits
To prevent false codes from recurring, establish thorough documentation, meticulous change logs, and regular audits as core preventive practices. You’ll set up clear templates for every change, defining purpose, expected impact, risk, and validation steps. Document the who, what, when, and why, so future reviews are decisive and fast. Emphasize documentation best practices: consistent formatting, version control, and accessible indexing, so every team member can locate critical details without hunting. Change log importance cannot be overstated: record every tweak, patch, or configuration shift with timestamps and rollback options. Regular audits validate that procedures stay aligned with evolving tools, standards, and compliance needs. Build automated reminders and dashboards to track gaps, overdue reviews, and unresolved inconsistencies. This disciplined routine fosters autonomy and confidence, enabling you to act decisively when anomalies surface. Stay proactive, precise, and transparent, and you’ll reduce drift and preserve system harmony.
Recovery and Long-Term Mitigation: Stopping Reoccurrence of False Codes
Building on the discipline of documentation and audits, the focus now shifts to recovery and long-term mitigation to stop false codes from reoccurring. You’ll implement a disciplined cycle that identifies, verifies, and stabilizes causes while preserving freedom to iterate. Focus on actionable steps that prevent regressing patterns and empower you to act quickly when new signals appear.
Building a disciplined cycle to identify, verify, and stabilize causes, preventing regression while staying ready to act on new signals.
1) Perform targeted error analysis to distinguish real failures from noise, then document findings for future audits.
2) Conduct a thorough code review to spot drift, unsafe assumptions, and integration gaps that could reintroduce false codes.
3) Plan system updates with minimal downtime, testing roles, and rollback options to maintain control and confidence.
4) Identify the root cause, implement a durable corrective, and monitor metrics to confirm sustained improvement.
This approach keeps you proactive, precise, and ever-ready to adapt without sacrificing autonomy.
Frequently Asked Questions
How Do False Codes Differ Across Hardware Platforms?
False codes differ across hardware platforms due to architecture and sensor interpretations; you’ll see variance in error naming, thresholds, and timing. You’ll need to map each platform’s codes to a common meaning before acting. When you compare, consider hardware discrepancies and how code interpretation may shift under different firmware. You stay proactive, documenting mismatches, testing across devices, and adjusting diagnostics so you’re always aligned with the actual fault rather than a mislabeled alert.
What Signs Indicate Phantom Errors in Toolchains?
Phantom errors in toolchains show up as inconsistent builds, intermittent failures, or logs that jump around without code changes. You’ll notice mismatched tool versions, unexpected header or symbol mismatches, and regressions reappearing after clean builds. These signs point to toolchains compatibility issues. Don’t panic: systematically verify compiler, linker, and environment versions, rework PATH and flags, run clean builds, and isolate the failing step. Stay precise, proactive, and confident as you restore stability.
Which Logs Best Reveal Misreported Diagnostic Codes?
Yes—the logs that best reveal misreported diagnostic codes are your error logs from the CI/CD pipeline and local tool runs, plus the verbose traces from diagnostic tools. You should correlate timestamps, tool IDs, and code states to pinpoint mismatches. Proactively export these logs, filter by anomaly keywords, and compare results across environments. Stay precise, systematized, and free-minded: treat every mismatch as actionable data, not noise.
How Can We Validate Cross-Tool Firmware Updates Safely?
You can validate cross-tool firmware updates safely by following a precise, methodical process with clear checkpoints. Start with a sandboxed testbed, then apply firmware validation methods that compare checksums, hashes, and behavioral baselines. Use safe update practices: staged deployments, rollback plans, and automated health monitoring. You’ll feel empowered, proofing compatibility before production. Track anomalies, document results, and maintain traceability. Your freedom hinges on disciplined testing, repeatable steps, and proactive risk mitigation.
What Metrics Quantify Improvement After Remediation Efforts?
Remediation success hinges on concrete performance metrics. You measure defect reduction, false-code elimination rate, and repeat incident frequency to quantify improvement. Track mean time to detection, mean time to remediation, and test coverage expansion after updates. You’ll compare pre- and post-remediation baselines, validating with control groups where possible. Use dashboards that emphasize trendlines over time, focus on stability, and set clear thresholds. This disciplined approach gives you freedom to optimize without guessing.




